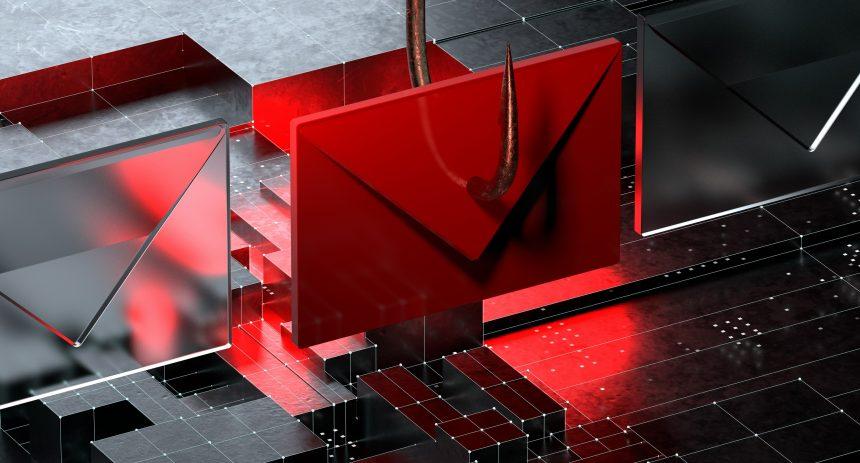
The Nature and Form of Phishing Scams
Phishing scams have become a pervasive threat in today’s digital age. These scams typically manifest as fraudulent communications, often in the form of emails, that appear to come from reputable sources. The primary aim of phishing scams is to trick recipients into divulging sensitive information such as passwords, credit card numbers, or other personal details. These scams often employ deceptive tactics, mimicking legitimate entities to gain the trust of unsuspecting victims.
Phishing scams infiltrate systems through various methods, including malicious email attachments, deceptive links, and fake websites. Once an individual falls for the scam, their system can become compromised, leading to potential identity theft, financial loss, and further malware infections.
The General Purpose of Phishing Threats
The primary objective of phishing threats is to gain unauthorized access to sensitive information. This information can be used for various malicious purposes, such as stealing money, committing identity theft, or conducting further cyberattacks. Infiltrating systems via phishing scams can also allow attackers to install malware, which can then be used to monitor activities, steal additional data, or even control the infected system remotely.
Legal Right to Claim Estate Email Scam
One particularly insidious example of a phishing scam is the “Legal Right to Claim Estate” email scam. This scam purports to inform the recipient that they have a legal right to claim an estate, attempting to lure them into providing personal information or clicking on malicious links.
Details of the Scam
- Instructions: The email typically instructs the recipient to provide personal information or follow a link to claim their supposed inheritance.
- Deceptive Tactics: The email may include official-sounding language and fake legal documentation to add legitimacy.
The purpose of this scam is to exploit individuals’ curiosity and greed, leading them to divulge sensitive information or download malware. Common reasons individuals encounter this scam include subscribing to dubious mailing lists, weak email security settings, and clicking on links from unknown sources.
Text presented in the “Legal Right To Claim Estate” spam email letter:
Subject: -Very Good News –
Dear friend,
I have a client who died of the Coronavirus pandemic in Wuhan China, unfortunately, he has no family that can stand as relatives to claim his properties and shares worth about $29,000,000.00 and the money at the bank to the tune of $14,700,000.00.
As his personal legal representative, I am in possession of his primary documents and for all of his property and financial documents.
I’m searching for someone who can stand as a relative so that he has the legal right to stand as next of kin and claim his estate. I will prepare every legal document necessary to make it a success in the least possible time. You can get up to 40% of the cost of the properties and shares ,
Regards,
Marco Va
Please send copy of your response to jebrehardt@outlook.com
Similar Threats
Similar phishing threats include:
- Fake IRS or tax refund emails
- Lottery or prize-winning notifications
- Emails claiming to be from financial institutions requesting account verification
These scams share a common theme of attempting to trick the recipient into providing personal information or clicking on malicious links.
Comprehensive Removal Guide
If you suspect your system has been compromised by the “Legal Right to Claim Estate” email scam, follow these detailed steps to remove any associated malware:
- Disconnect from the Internet: Unplug your Ethernet cable or disconnect from your Wi-Fi network to prevent further data transmission.
- Enter Safe Mode:
- Restart your computer and press
F8(or the appropriate key for your system) before Windows starts loading. - Select “Safe Mode with Networking” from the options menu.
- Restart your computer and press
- Install and Run Antivirus Software: Run a full system scan with a reputable anti-malware program to identify and remove any malware.
- Remove Suspicious Programs:
- Go to
Control Panel>Programs and Features. - Uninstall any unfamiliar or suspicious programs.
- Go to
- Delete Temporary Files:
- Use the Disk Cleanup tool (
Start>All Programs>Accessories>System Tools>Disk Cleanup). - Check all the boxes and click “OK” to delete temporary files.
- Use the Disk Cleanup tool (
- Check Browser Extensions:
- Remove any unfamiliar browser extensions.
- In Chrome:
Menu>More tools>Extensions. - In Firefox:
Menu>Add-ons>Extensions.
- Reset Browser Settings:
- In Chrome:
Settings>Advanced>Reset settings. - In Firefox:
Help>Troubleshooting Information>Refresh Firefox.
- In Chrome:
- Update Software and Operating System: Ensure all your software and operating system are up-to-date to patch security vulnerabilities.
- Change Passwords: Change passwords for all online accounts, especially those related to financial information.
- Monitor Accounts for Unusual Activity: Keep an eye on your financial accounts for any unauthorized transactions.
Preventative Measures
To avoid falling victim to phishing scams in the future:
- Be Skeptical of Unsolicited Emails: Do not trust emails from unknown sources or those that request sensitive information.
- Verify the Sender: Check the sender’s email address carefully for discrepancies.
- Hover Over Links: Before clicking, hover over links to see the actual URL.
- Use Strong Passwords: Implement strong, unique passwords for different accounts.
- Enable Two-Factor Authentication: Add an extra layer of security to your accounts.
- Keep Software Updated: Regularly update your operating system and applications to protect against security vulnerabilities.
- Educate Yourself and Others: Stay informed about the latest phishing tactics and share this knowledge with friends and family.
By following the steps outlined above and remaining vigilant, you can protect yourself from phishing scams and maintain the security of your personal information.
If you are still having trouble, consider contacting remote technical support options.