What is Luck (MedusaLocker) Ransomware?
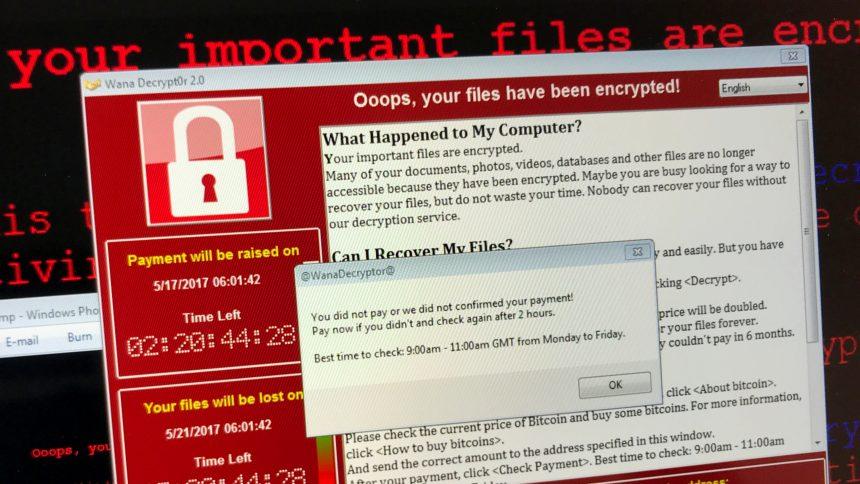
Luck (MedusaLocker) is a ransomware-type malware designed to encrypt victims’ files and demand a ransom for decryption. As part of the MedusaLocker ransomware family, Luck operates by infiltrating systems, encrypting files, and coercing victims into paying large sums of money. This malware appends a “.luck_06” extension to encrypted files, such as converting “1.jpg” into “1.jpg.luck_06.” Variants of Luck ransomware may append different numbers in the file extension.
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
After encryption, the ransomware leaves a ransom note in an HTML file titled “How_to_back_files.html.” The note warns victims that their company network has been compromised, their files encrypted using RSA and AES algorithms, and their sensitive data stolen. Victims are urged not to modify the files or use third-party decryption tools, as this might make data recovery impossible. The ransom demand escalates if the victim delays contacting the cybercriminals, and failure to comply can lead to stolen data being publicly released or sold.
How Luck (MedusaLocker) Ransomware Operates
Luck ransomware uses a combination of advanced encryption algorithms—RSA and AES—to ensure the locked files remain inaccessible without the proper decryption keys. Here are the key stages of its operation:
- System Infiltration: Luck gains access to systems through phishing emails, malicious attachments, software vulnerabilities, or fake updates.
- File Encryption: Once executed, it encrypts files across the system, targeting documents, images, videos, and other valuable data.
- Ransom Note Deployment: After encryption, the ransomware delivers a ransom note that outlines the attack details and provides instructions for contacting the attackers. Victims are threatened with increased ransom demands if they delay.
- Data Theft: In addition to encryption, Luck steals sensitive data and uses the threat of releasing this information as leverage to pressure victims into payment.
- Ransom Negotiation: The attackers claim to offer a decryption test by unlocking a few files to prove their ability to decrypt the data. Payment is demanded in cryptocurrency, and there are no guarantees that decryption tools will be delivered even after payment.
Symptoms of Infection
- Previously accessible files are now encrypted and display a “.luck_06” extension.
- A ransom note file titled “How_to_back_files.html” appears on the desktop and affected directories.
- Warnings discourage tampering with the files or using alternative decryption solutions.
- Cybercriminal contact information, such as recovery012012@onionmail.org, is provided for negotiations.
Detection and Security Risks
Luck ransomware is detected by various antivirus and anti-malware tools under different names, including:
- Avast: Gen:Variant.Ransom.MedusaLocker.65
- ESET-NOD32: A Variant Of Win64/Filecoder.MedusaLock
- Kaspersky: HEUR:Trojan-Ransom.Win32.Generic
- Microsoft: Trojan:Win64/Filecoder.ARA!MTB
Aside from file encryption, the presence of ransomware increases the risk of additional malware infections, such as trojans designed to steal sensitive information like passwords.
Removal Guide
Remove annoying malware threats like this one in seconds!
Scan Your Computer for Free with SpyHunter
Download SpyHunter now, and scan your computer for this and other cybersecurity threats for free!
Step 1: Disconnect the System from the Network
- Immediately isolate the infected device to prevent the ransomware from spreading to other devices in the network.
- Turn off Wi-Fi and disconnect any external drives or storage devices.
Step 2: Boot into Safe Mode
- Restart the computer and press the F8 key repeatedly during startup.
- Select Safe Mode with Networking from the Advanced Boot Options menu.
Step 3: Use a Reliable Anti-Malware Tool
- Download and install a trusted anti-malware program such as SpyHunter.
- Perform a full system scan to detect and remove Luck ransomware and other associated threats.
Step 4: Restore System Files
If backups are available, restore your data from a secure source. Do not connect backup devices until the system is fully cleaned. Without backups, file recovery might not be possible unless the decryption keys are obtained.
Step 5: Reinstall the Operating System (Optional)
In severe cases where ransomware has caused extensive damage, consider formatting the hard drive and reinstalling the operating system to eliminate residual malware completely.
Prevention Tips to Avoid Ransomware Infections
- Maintain Regular Backups: Store backups on remote servers or offline storage devices. Ensure backups are updated frequently.
- Use Robust Security Tools: Install reputable antivirus and anti-malware programs and keep them updated.
- Exercise Caution with Emails: Avoid opening unsolicited email attachments or clicking on suspicious links.
- Update Software Regularly: Ensure that the operating system and all applications are up to date to minimize vulnerabilities.
- Disable Macros in Documents: Configure office applications to block macros by default, as they are a common vector for ransomware.
- Be Wary of Free Software and P2P Networks: Avoid downloading pirated software or media files from untrustworthy sources.
- Use Strong Passwords: Employ unique, complex passwords for all accounts and enable two-factor authentication wherever possible.
Conclusion
Luck (MedusaLocker) ransomware represents a significant threat to individuals and organizations alike. By encrypting data and demanding ransom payments, it causes substantial financial and emotional distress. While removal of the malware can prevent further encryption, it does not guarantee file recovery unless backups are available.
Prevention remains the best defense against ransomware attacks. Employ robust security practices, keep backups in multiple locations, and educate yourself about cyber threats to reduce the likelihood of future infections.
Text presented in the ransom message:
YOUR PERSONAL ID:
–
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!
Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.
No software available on internet can help you. We are the only ones able to
solve your problem.
We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..
We only seek money and our goal is not to damage your reputation or prevent
your business from running.
You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.
Contact us for price and get decryption software.
email:
recovery012012@onionmail.org
TOX ID:
3D741563254E906DE5512FAE8E7F53FB453672297C2F159BE22736CBCE347F4E892207593F09
* To contact us, create a new free email account on the site: protonmail.com
IF YOU DON’T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.