Understanding Trojan Horse Malware: The POSetup Threat
Trojan horse malware, often simply called "Trojans," is a type of malicious…
Line Virus Adware: An Introduction
Adware, short for "advertising-supported software," is a type of malware designed to…
AdultTime.com Ads: Revealing the Threat Posed by Adware
Adware is a type of malware designed to deliver unwanted advertisements to…
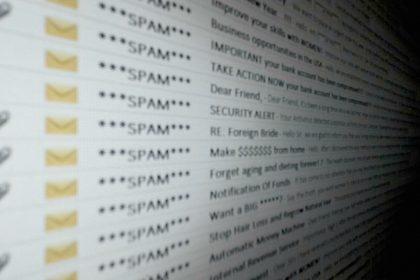
“Confirm That This Is Your Valid Email Address” Phishing Scam
Phishing scams are a pervasive threat in today’s digital landscape, designed to…
“I’ve Got Access to Your Smartphone” Email Scam: A Comprehensive Guide to Protecting Yourself
Phishing scams are a constant threat in today’s digital world, evolving with…
Missed Call Voicemail Alert Scam: A Phishing Threat to Watch Out For
Phishing scams have become increasingly sophisticated, using clever tactics to deceive users…
Rothschild Foundation Email Scam: A Dangerous Phishing Threat and How to Protect Yourself
Phishing scams have become an increasingly common threat, targeting individuals and businesses…
“Your Device Is at Risk” Pop-up Scam on Mac: How to Remove It and Protect Your System
The "Your Device Is at Risk" pop-up scam is one of the…
Hack.TL Ver U99 B Buzz: A Form of Adware that Affects Users’ Systems
Adware is a form of malware designed to deliver unwanted advertisements on…
Trojan.PowerShell.CoinStealer.RPMTB: Malware: Understanding the Threat
Trojans, or Trojan Horse malware, represent one of the most dangerous forms…