Trojan:BAT/Starter.G!Ink – What It Is, How to Remove It, and Prevention Tips
Trojan:BAT/Starter.G!Ink is a stealthy and highly dangerous malware that uses the Windows…
InvisibleFerret Backdoor Malware: Understanding, Removing, and Preventing Future Infections
InvisibleFerret is a sophisticated Python-based backdoor malware associated with North Korean threat…
Removing the Rotq App Threat
The Rotq App is a suspicious application flagged by multiple security vendors…
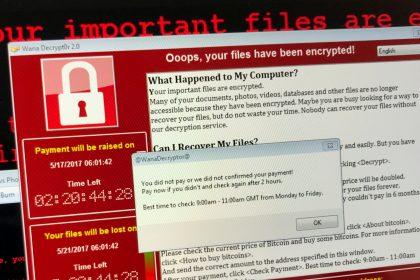
BlackPanther Ransomware
BlackPanther is a dangerous ransomware strain that locks your files by encrypting…
LulzDecryptor Ransomware: Threat Analysis, Removal, and Prevention
Understanding LulzDecryptor Ransomware The LulzDecryptor Ransomware is a file-locking Trojan designed to…
Hyena Ransomware: Analysis and Removal Guide
Hyena ransomware, a member of the MedusaLocker family, is a dangerous malware…
Removing WantToCry Ransomware and Preventing Future Infections
Ransomware attacks are among the most destructive cyber threats faced by individuals…
opdomain22[.]online: Removal Guide & Prevention Tips
opdomain22online is a deceptive website designed to promote scams and expose users…
Mobitera[.]online: Detection, Removal, and Prevention
The internet is full of deceptive websites aiming to exploit users for…
What Is HEUR.Malware.Misc.Packed.Generic?
HEUR.Malware.Misc.Packed.Generic is a heuristic detection label used by antivirus software to identify…