Re-Captha Version 3.263: A New Cyber Threat Emerges
In the ever-evolving landscape of cybersecurity threats, a new menace has emerged,…
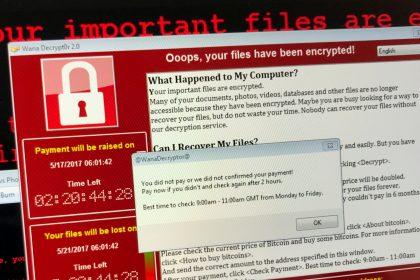
RinCrypt 3.0 Ransomware: A Menace in the Cyber Realm
RinCrypt 3.0 stands out, among its ilk, as a particularly insidious strain…
Beware of the “Switch to New Server” Email Scam: A Cyber Threat Alert
In our age, dominated by digital communications, email scams continue to be…
Robaj Ransomware: Removal Guide and Prevention Tips
Ransomware continues to be a significant concern for individuals and organizations alike.…
“Agreement Update” Email Scam: A Deceptive Cyber Threat
Cybercriminals are constantly devising new methods to exploit unsuspecting individuals and organizations.…
ReCaptcha Version 3.223: A Stealthy Cyber Threat
A new menace has emerged, lurking in the shadows of our digital…
Bitcoin Email Virus: A Comprehensive Guide
In the digital age, cyber threats come in various forms, and one…
Alructisit Malware: Threat Analysis and Removal Guide
In the vast landscape of cyber threats, the emergence of the Alructisit…
Diamond Duck Crypto Ransomware: Removal Guide and Prevention Measures
From a multitude of variants, Diamond Duck Crypto Ransomware has emerged as…
Huntransomware: A Menace to Cyber Security
In recent times, one name has been causing significant concern among security…