Re-Captcha Version 5.1 Browser Hijacker: A Comprehensive Guide
Browser hijackers represent a particular form of malware designed to manipulate and…
Purgat0ry Ransomware: Preventing and Removing Encryption Attacks
Ransomware is a malicious form of software designed to lock or encrypt…
Elpaco Team Ransomware: Defending Your System from Ransomware Threats
Ransomware is a form of malicious software designed to block access to…
8Base Chaos Ransomware: Understanding & Removing Ransomware
Ransomware is a form of malicious software designed to block access to…
PUP.Win32.GameHack: Understanding Potentially Unwanted Programs (PUPs)
Potentially Unwanted Programs (PUPs) are a type of malware that can significantly…
Salwyrr Launcher Malware: An Overview
The Salwyrr Launcher is a deceptive software that disguises itself as a…
Understanding and Addressing Prince Ransomware
Ransomware is a form of malicious software designed to block access to…
Cthulhu Stealer: A Dangerous Malware Threat and How to Remove It
In the ever-evolving landscape of cybersecurity threats, new and more sophisticated forms…
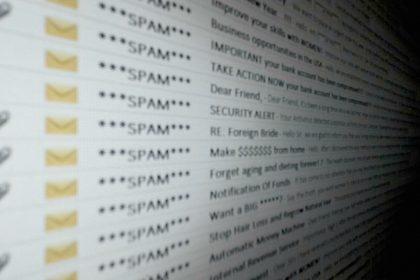
SharePoint ACH/Wire Authorization Email Scam: Avoiding Phishing Threats
Cybercriminals have evolved their tactics to become increasingly sophisticated, using a variety…
Beenbit Scam Removal
Cyber threats have become increasingly sophisticated, targeting users' personal information and system…