CAN Stealer Malware: Understanding and Removing the Threat
CAN Stealer is a sophisticated type of malware specifically designed to harvest…
Dzentime Virus: A Complete Removal Guide
Cyber threats continue to evolve, becoming more dangerous and sophisticated with each…
Understanding Trojan Horse Malware: The POSetup Threat
Trojan horse malware, often simply called "Trojans," is a type of malicious…
Line Virus Adware: An Introduction
Adware, short for "advertising-supported software," is a type of malware designed to…
Claim Eigen Scam: Detailed Overview and Removal Guide
The Claim Eigen scam is a deceptive and potentially harmful cyber threat…
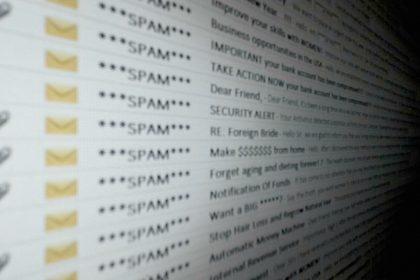
“Confirm That This Is Your Valid Email Address” Phishing Scam
Phishing scams are a pervasive threat in today’s digital landscape, designed to…
“Website Suspension in Progress” Phishing Scam: Fighting Email Scams
Phishing scams are deceptive tactics used by cybercriminals to trick individuals into…
Hack.TL Ver U99 B Buzz: A Form of Adware that Affects Users’ Systems
Adware is a form of malware designed to deliver unwanted advertisements on…
HLAS Virus Files: A Comprehensive Guide
Malware threats are becoming increasingly sophisticated, targeting unsuspecting users and wreaking havoc…
TL-Ver-T39-I-Buzz: Removal, Detection, and Prevention
New and sophisticated malware constantly emerges, posing significant risks to personal and…